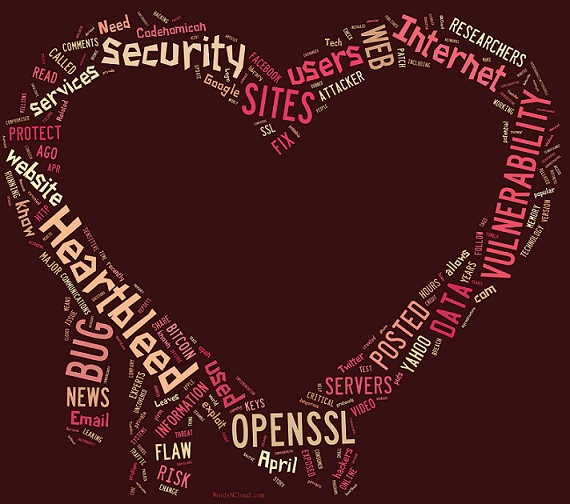
1st DO NOT CHANGE YOUR PASSWORD just yet. Keep reading to find out what to do. Heartbleed of very bad and critical vulnerability in OpenSSL. SSL is widely used by a lot of websites. Most banks do not use OpenSSL. However, you go to more than banks online don’t you? The coding error was in OpenSSL 1.0.1 that was released way back in 2012. The vulnerability lets a hacker trick the website into handing out some of memory its memory over and over again. The memory has the website’s sensitive information in it and indirectly your information too. The server private keys for encryption of the website is part of the information the Heartbleed hands out. So if someone gets a hold of the encryption keys of the website they can clone your site and trick people to think they are legit. Yo would see the little lock as if it is a safe site. So how can you protect yourself or see if you were comprised? Click the SSL Sever Test link to test the website of your choice. If it is fixed go ahead and change your password. If it is not fixed yet. DO NOT CHANGE YOUR PASSWORD just yet.
SSL Server Test
The above link is ssllabs.com/ssltest and is a free online service performs a deep analysis of the configuration of any SSL web server on the public Internet. Please note that the information you submit here is used only to provide you the service. We don’t use the domain names or the test results, and we never will.

If the site is venerable, WAIT for it to get fix before changing your password. Keep checking in daily, hourly if you wish. Also this would be a great time to use a Password manager such as Roboform or Last Pass. You should assume that your password has been compromised. It will continue to be compromised until the site issues a patch, replaces their old encryption key as well as certificates, and revokes the old certificates they don’t used by hackers. This is a very big deal. Estimates are 2/3 of the internet has been compromised.
Until the problem is fixed it’s not a good idea to change every password everywhere because it allows people who are acting in a criminal manner to see the passwords. So you could have exposure again and again and again until the problem is fixed.
Update: Cisco Systems and Juniper Networks have admitted that their routers are at risk. Check to see if your Juniper Networks device is affected by clicking > here and here. If you have a Cisco Systems router you can check by clicking here. Although both companies are working on patches for the affected hardware no update is out just yet.